RISK & STRATEGY CONSULTING
Services :
Security governance implementation
Security policies
Security framework (NIST CSF)
Cyber maturity assessment (CMMC)
ISO 27001 Gap analysis
Support and advice to managers
Security strategy development
The security outcome is highly dependent on the ability of managers to adopt the security strategy of the company or group they manage. Security is at the heart of the digital transformation, and it is also central to companies that are already fully embedded or born in the digital era.
There are an incredible number of highly relevant and effective technical solutions, but security is above all an integrated system that relies on men and women. Without systemic integration, there is inevitably a distortion between expenditure and the expected result.
Security is therefore an organisational principle relying on human expertise, capable of orchestrating the tools adapted to the needs of the company and its strategy. In this context, managers must guarantee that the means to properly adapt culture and resources are provided in order to adopt the security strategies that they are responsible for developing.
Understanding governance threats and issues
Identifying security issues is relatively easy for managers who consider whether they are well supported by internal and/or external advisers. The Chief Executive Officer and the members of the Board are very aware of the availability and efficiency requirements of critical elements upon which the success of their company is based; they invest time and resources in them.
Challenges in expertise at General Management and Board level are generally more related to understanding the threats and requirements in terms of cyber governance.
La mission de CAP ’s mission is to enable managers to understand the principles and conditions for the proper adoption of cyber frameworks in their company, so that they can decide and commit.
Adopting the right security governance strategies
Adopting the right governance strategies is critical to maintaining the right balance between security-related spending and expected outcomes. Despite this being a crucial issue, it is often neglected, resulting in many failures or imposed changes of course. Sometimes this results in an inability to effectively counter attacks even though the dedicated budgets are significant.
La mission de CAP ’s mission is therefore to adopt the right governance strategies so that, when the destination and the course have been set, decisions can be taken.
Setting a cyber budget adapted to your needs
The security component can no longer be ignored and many companies do not have a budget line dedicated to security or its governance. Yet security expenditure exists, although it is often complicated or even impossible to measure its effectiveness and its relevance even less. This is how companies end up in a situation where, although the expenditure exists, it is often inadequate and even more often ill-suited to the company’s real challenges and needs.
CAP recommends a risk-based budgetary approach rather than focusing on maturity models or “state of the art” targets. Using this approach, CAP supports managers in facilitating realistic, efficient and usable budget sizing.
CYBER DUE DILIGENCE
Services :
Offre modulaire d’analyse financière et risque relative à la sécurité, dans le cadre d’une fusion ou acquisition ainsi que celui d’une vente.
The value of a company is no longer limited to its financial or social balance sheet. A company’s ability to withstand malicious acts has become an essential component of a company’s price analysis. Acquiring a company as part of a vertical growth policy therefore requires a clear understanding of the security issues that a company is capable of mastering. CAP has built a multi-level offer enabling any company targeting the acquisition of another company to assess the actual cost of its acquisition and thus determine a maximum purchase price adapted to the reality of the situation. For the purchaser, it is therefore a tool to help with the decision to buy at the right price and for the seller a means to facilitate the sale at the best price.
• Assessing the cyber risk of an acquisition target
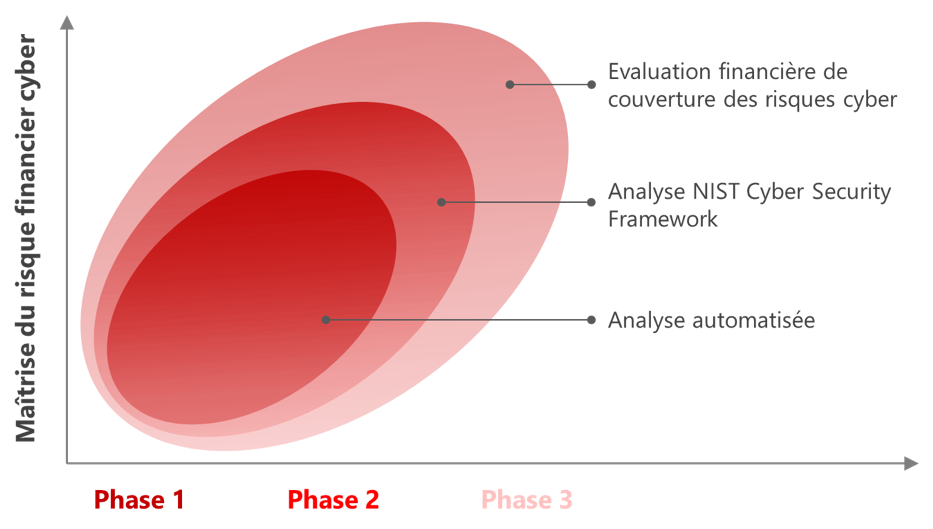
This is a 3-phase approach, each of which is self-contained. These phases offer different levels of guarantee. They further limit the risks associated with the acquisition at each level and give the purchaser a better understanding of the costs that it will need to devote at each level if it wishes to structure this acquisition in such a way that any cyber risks are covered.
PHASE 1
Automated external analysis requiring no intervention from the acquisition target. It is not necessary to inform the acquisition target.
PHASE 2
Includes phase 1 + an analysis requiring limited cooperation from the acquisition target. This analysis takes 3 days at the acquisition target’s premises. It is based on the development of a NIST cyber framework or the evaluation according to CMMC maturity model, fully managed by CAP.
PHASE 3
Includes phases 1 and 2 + an assessment of the restructuring cost of the acquisition target based on criteria predetermined with the purchaser. This phase does not require the intervention or solicitation of the acquisition target.
• Reassuring financial partners or a future buyer of your cyber capabilities
If you are a seller, CAP proposes to score your cyber maturity in 3 phases, each of which is self-contained. Each phase gives each level a little more credibility as to your ability to control cyber risks. They enable the purchaser to assess your sale price and limit its risk at the time of acquisition.
PHASE 1
Automated external analysis requiring no intervention on your part. We produce an explicit score relating to your exposure to cyber risks.
PHASE 2
Includes phase 1 + an analysis requiring limited support from you. This analysis usually takes 3 days for one or more of your IT/ISS contacts. It is based on the development of a NIST cyber framework or a CMMC maturity model.
PHASE 3
Includes phases 1 and 2 + a restructuring cost assessment allowing you to improve your score. This phase requires very limited intervention (1 to 3 man-days) and includes the participation of the CEO, CFO and ISD.
